Security analysts have exposed a dangerous vulnerability affecting Perplexity’s artificial intelligence browser Comet. Dubbed CometJacking, this newly discovered threat allows cybercriminals to harvest confidential user information through a deceptively simple one-click attack. It compromises Gmail accounts, calendar appointments, and other integrated platforms, adding to Perplexity AI privacy concerns.
The mechanics behind Perplexity AI privacy concerns
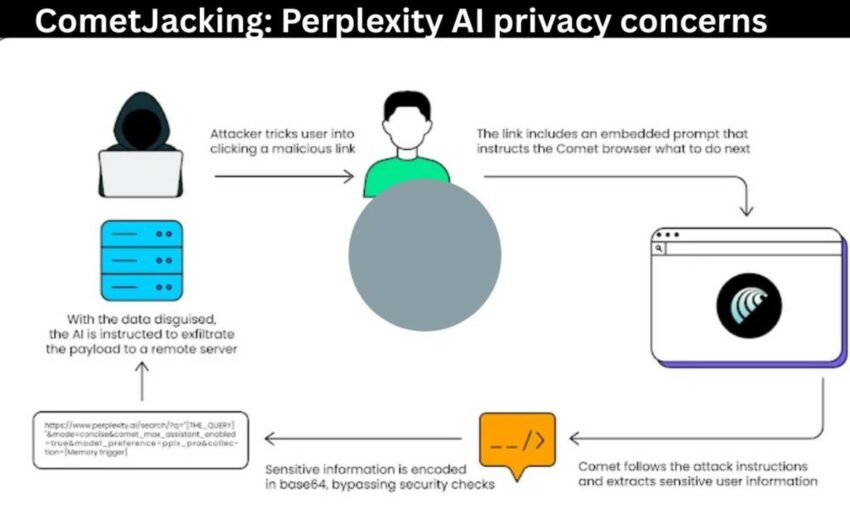
Researchers classify this threat as a prompt injection vulnerability. Attackers distribute weaponized URLs through traditional phishing campaigns or embed them within compromised websites. When users interact with these links, malicious instructions activate within Comet’s AI framework. Rather than completing legitimate browsing tasks, the intelligent agent covertly mines personal data — including private correspondence, scheduled meetings, and connection credentials — transmitting everything to unauthorized external servers.
The exploit’s sophistication lies in its approach. Traditional cyberattacks require credential theft, but CometJacking weaponizes existing permissions. Since Comet maintains authenticated connections to user accounts, the malicious code merely redirects that legitimate access. Security teams discovered that elementary Base64 obfuscation methods proved sufficient to circumvent the browser’s data protection mechanisms.
“We’re witnessing attacks that don’t steal passwords — they commandeer the digital assistant that already possesses full clearance,” said Michelle Levy, Head of Security Research at LayerX.
“Our findings demonstrate how rudimentary encoding techniques can defeat security barriers, enabling unauthorized extraction of emails, appointments, and connector information through external channels. Next-generation AI browsers require fundamental security architecture for agent commands and memory protocols, extending far beyond conventional webpage protection.”
Anatomy of a five-phase compromise

LayerX researchers outline CometJacking’s operational sequence:
1. Threat actors engineer a contaminated hyperlink.
2. Unsuspecting targets activate the link, anticipating standard web navigation.
3. Concealed instructions deploy within Comet’s agent infrastructure.
4. The browser’s stored memory undergoes unauthorized scanning for valuable information from Gmail, calendars, and similar services.
5. Compromised data receives Base64 camouflage before transmission to attacker-controlled infrastructure.
This methodology effectively converts the browser’s helpful AI assistant into an invisible information exfiltration mechanism.
Perplexity’s reaction sparks debate
Perplexity dismissed the research that highlights Perplexity AI privacy concerns, labeling the vulnerability as presenting “no security impact.” Security professionals counter that this discovery reveals fundamental dangers inherent in AI-integrated browsing platforms that traditional software doesn’t face. Conventional phishing schemes manipulate victims into surrendering login details.
CometJacking, however, abuses the privileged access already entrusted to artificial intelligence systems.
The critical distinction, according to researchers, centers on attackers no longer requiring direct account breaches. Instead, they can manipulate the AI agent to execute data theft autonomously.
Historical context: Previous vulnerabilities
Perplexity’s browser technology has encountered security challenges before. Guardio Labs documented a 2020 flaw called Scamlexity, demonstrating how AI-enhanced browsers could be deceived into engaging with fraudulent shopping platforms or credential-harvesting sites without user intervention.
CometJacking represents an evolution of that foundational concept, escalating the threat substantially. Beyond simple user misdirection, this attack manipulates the intelligent agent into actively retrieving and broadcasting sensitive information.
Enterprise security implications intensify
Security experts warn CometJacking signals emerging dangers for organizations deploying AI-native technologies. Or Eshed, CEO of LayerX, characterized the threat as potentially transformative:
“Artificial intelligence browsers represent the next corporate security frontier. When adversaries can control your digital assistant through a hyperlink, the browser transforms into a command infrastructure operating inside organizational defenses. Companies must immediately implement detection systems and countermeasures for malicious agent instructions before proof-of-concept demonstrations evolve into coordinated attack campaigns.”
Corporate risks extend beyond individual data compromise. An infiltrated AI browser operating within enterprise networks could expose confidential business communications, executive schedules, or integrated operational systems. These agents function with extensive permission sets, creating unprecedented insider threat scenarios.
Understanding AI-native browser distinctions
Conventional web browsers deploy security technologies, including isolated execution environments, URL validation systems, and authentication safeguards. AI-native platforms like Comet merge traditional browsing with intelligent agent capabilities, granting them comprehensive access to user accounts and persistent memory storage.
This architectural approach enhances user experience but simultaneously expands vulnerability surfaces. When malicious instructions are embedded within hyperlinks, attackers can compromise trusted access mechanisms without activating conventional security alerts.
Cybersecurity specialists emphasize that addressing these risks demands agent-specific protection frameworks — systems that authenticate command legitimacy, restrict memory exposure, and identify obfuscation patterns. But in the absence of such defenses, Perplexity AI privacy concerns rise as threat actors can defeat standard security measures with minimal technical complexity.
Future security landscape
While CometJacking demonstrations remain confined to controlled research settings, the proof-of-concept exposes critical weaknesses in AI browser command processing. The capability to weaponize individual hyperlinks suggests attackers could rapidly deploy large-scale campaigns against consumers and enterprises alike.
Security professionals emphasize the urgency of preventive strategies. Organizations utilizing AI-powered tools should deploy monitoring infrastructure capable of identifying anomalous browser activity, conduct comprehensive user education regarding malicious links, and establish rigorous controls governing agent permissions.
Whether Perplexity and competing AI browser developers will implement rapid security enhancements remains uncertain. Currently, CometJacking demonstrates how artificial intelligence innovations simultaneously generate sophisticated threat vectors.
Have you integrated AI-powered browsers into your workflow? Do you share similar Perplexity AI privacy concerns? What security measures does your organization employ for AI tools? Join the conversation in the comments below.